July 12, 2018 by Siobhan Climer
The American Institute of Certified Public Accountants (AICPA) set forth the Statement on Standards for Attestation Engagements (SSAE 18 Audit Report) to formalize the auditing process for Certified Public Accountants (CPAs). An attest engagement is slightly broader than an audit in that it assesses both what management claims is occurring and the actual reality, especially as it relates to third-party vendors. Furthermore, audits remain private while the results of SSAEs are public. Mindsight values transparency, which is why we seek out opportunities for respected third parties to assess and comment on our client-focused practice.
SAS 70 To SSAE 16 To SSAE 18
The SSAE 18 Audit Report is a modified version of previous attestation engagements, all of which seek to certify third-party vendor risk management. Mindsight is an industry leader in assessing and managing third-party vendor risks, with CTO Jason Wankovsky leading a panelist discussion on vendor security at a recent CAMP IT event. Before the SSAE 18, companies used the SAS 70 and the SSAE 16 (modified requirements for the SOC 1 report).
As far as changes to requirements go, the SSAE 18 expanded the attestation examination by differentiating the SOC 1 report from the SSAE, providing additional criteria, and matching expanding needs of the market. The new controls monitored by the SSAE 18 Audit Report require additional effort on the part of the service organization, but passing this audit means customers can fully rely on the company’s credibility.
The Complex Network Of Service Organizations And Subservice Organizations
A service organization is, simply, an enterprise that provides a service: from cloud hosting to network infrastructure. For example, Mindsight provides managed services and consulting with data centers, cloud computing, network infrastructure, contact center solutions, disaster recovery and backups, collaboration tools and applications, and full IT roadmaps.
That’s a lot to do! And that is part of the reason we work with other service organizations, sometimes called subservice organizations or third-party vendors, to ensure we fully meet the needs of our clients.
The question then is how can our clients trust that the organizations we work with will also meet the standards of expertise, security, and trust – those very qualities on which Mindsight places the greatest emphasis?
The SSAE 18 Audit Report takes these organizations into account, ensuring that Mindsight’s clients can trust that both Mindsight – and the subservice organizations with which we work – are serious about what we say. It is a complex network, and the SSAE 18 identifies all the moving parts before assessing each one both independently and as part of the whole.
What Is Covered In An SSAE 18 Audit Report?
There are seven main areas identified in the SSAE 18, which are then followed up with recommendations. The recent changes to the SSAE 18 include the following assessment details:
 Risk Assessment – Assessment of service organization controls and identification of all associated subservice organizations.
Risk Assessment – Assessment of service organization controls and identification of all associated subservice organizations.
Output Reports – Examination of protocols relating to all external communications, including financial reports and client communications.
Periodic Subservice Meetings – Analysis of service organizations’ communications with subservice organizations.
Regular Subservice Site Visits – Analysis of service organizations’ external site visits to confirm subservice organization claims.
Test Subservice Controls – Verification of subservice organization controls through regular testing.
Subservice Organization Document Reviews – Analysis of all subservice organization SOC 1 or SOC 2 reports.
Monitor Subservice External Communications – Analysis of subservice organizations’ external communications, from financial reports to customer complaints.
The SSAE 18 Audit Report identifies if the service organization is engaging in these activities. It ensures that companies are monitoring all third-party vendors. This means that when a client partners with an SSAE 18 AICPA certified organization like Mindsight, the third-party vendor risk analysis has already been performed.
Why It Matters
Back in 2014, Target was the victim of a large data breach that left over 40 million credit and debit cards exposed. How did such a large hack occur? Through a third-party HVAC vendor. Many companies use internet-connected HVAC (heating, ventilation, and air conditioning) systems, and it was through this system hackers accessed the point-of-sale (POS) systems and stole valuable personal credit information (PCI).
As it turns out, over 55,000 HVAC systems do not have adequate security.
How could this affect you?
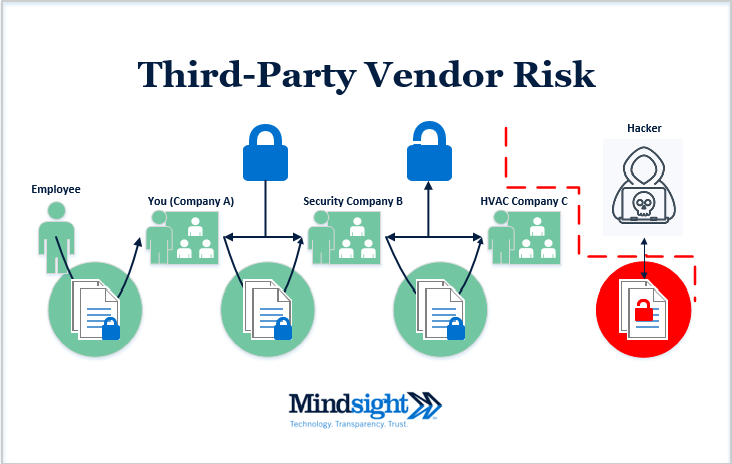
Let’s say you – Company A – perform background checks on your employees. You outsource this task to a security firm, Company B. Company B uses HVAC systems in their buildings and partners with company C. Company C uses internet-connected HVAC systems that are improperly secured and suffers an external cyber attack. What happens next? The personal information of any employee you submitted to Company B has been compromised (see Fig. 1).
Figure 1: Third-Party Vendor Risk: HVAC A-B-C Example
Sound complicated? It is. It’s a complex network.
By performing the SSAE 18 Audit Report, companies like Mindsight work with the independent auditor to identify, assess, and monitor third-party relationships, so our clients know that when we say Technology. Transparency. Trust. we really mean it.
Find out more about how Mindsight ensures your data is secure by contacting us today.
Like what you read?
About Mindsight
Mindsight, a Chicago IT services provider, is an extension of your team. Our culture is built on transparency and trust, and our team is made up of extraordinary people – the kinds of people you would hire. We have one of the largest expert-level engineering teams delivering the full spectrum of IT services and solutions, from cloud to infrastructure, collaboration to contact center. Our highly-certified engineers and process-oriented excellence have certainly been key to our success. But what really sets us apart is our straightforward and honest approach to every conversation, whether it is for an emerging business or global enterprise. Our customers rely on our thought leadership, responsiveness, and dedication to solving their toughest technology challenges.
Contact us at GoMindsight.com.
About The Author
Siobhan Climer, Science and Technology Writer for Mindsight, writes about technology trends in education, healthcare, and business. She previously taught STEM programs in elementary classrooms and museums, and writes extensively about cybersecurity, disaster recovery, cloud services, backups, data storage, network infrastructure, and the contact center. When she’s not writing tech, she’s writing fantasy, gardening, and exploring the world with her twin two-year old daughters. Find her on twitter @techtalksio.