October 19, 2021 by Siobhan Climer and Mishaal Khan
This article was originally published in August of 2019.
If we were to write a story on every reported data breach from the first three quarters of 2021, some poor person would be churning out 1,291 eerily similar stories. This is up by 17% from the same time period in 2020, and is on track to break records for data compromises in a calendar year.
Phishing and ransomware remain the top two most popular methods for hackers. Unfortunately, according to the Identity Theft Resource center, “There has been an increase in a lack of transparency in breach notices at both the organization and government level that, if it continues, could lead to a significant impact on individuals”.
Cool. Cool. Cool.
But who do these breaches really affect? Everyone. From business to healthcare, education to financial services, manufacturing to the public sector, data breaches – whether by malicious parties or ignorant users – are a threat to your business.
Data Breaches Impact Your Business – But How?
Financial
Certainly, there are both immediate – and hidden – financial costs to a data breach. A breached business needs to repay any stolen funds, compensate customers, and suffer a share value loss. A smart organization will also use this as the drive to develop data security and disaster recovery strategies, which requires financial investment.
Hidden costs, such as fines, public relations, legal fees, and regulatory punitive measures, may also lie in wait. Organizations affected by data breaches may be fined, especially if data is sensitive (PII, PHI). In the US, breached businesses are often the subject of lawsuits. In 2019, Equifax – which exposed over 143 million user accounts – was fined over $700 million (though whether that was significant is a matter of debate).
Reputation
 Customer loyalty and trust take a nose dive after a data breach. Your customers value their privacy, and they will perceive a data breach as a lack of respect for their data and privacy. Your business is trusted to be customer-first and focused on people over profits. 46% of organizations say they suffered damage to their reputation and brand value as a result of a breach.
Customer loyalty and trust take a nose dive after a data breach. Your customers value their privacy, and they will perceive a data breach as a lack of respect for their data and privacy. Your business is trusted to be customer-first and focused on people over profits. 46% of organizations say they suffered damage to their reputation and brand value as a result of a breach.
The potential also exists for internal-only communications to be released as the result of a data breach. Imagine how your customers may perceive hastily-sent email exchanges or archaic sales’ records.
Intellectual Property
The product blueprints, business strategies, and engineered solutions you have are some of your most valuable assets. Your trade secrets are what give you an advantage over your competitors, and some may not hesitate to use breached intellectual property against you.
Protect Your Business Before You Are Breached
You need security expertise that understands the threats to your business, and a disaster recovery strategy that accounts for cyber resiliency and data loss. Our experts will help you do the following:
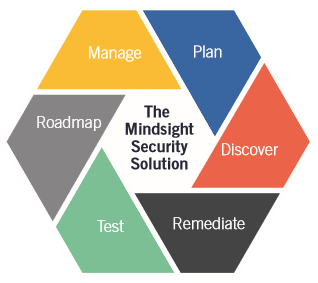 Plan: take the time to fully understand your security priorities and identify solutions custom-fit to your needs.
Plan: take the time to fully understand your security priorities and identify solutions custom-fit to your needs.
Discover: assess your current security posture and reviews configurations to create a strategic security solution that meets your business objectives.
Remediate: implement appropriate security controls and review policies and procedures while hardening your security architecture to protect against the most relevant threats to your business.
Test: break in, test, and infiltrate the layers of security to identify additional gaps and validate security controls.
Roadmap: create a strategy that prepares you for tomorrow’s threats. This hardened security framework helps you respond proactively to pervasive market rises.
Manage: ensure the continued management of your security posture so you are confident you can respond to the most imminent threats.
Want help? Mindsight’s security and disaster recovery experts are just a click away.
Contact us today to discuss how to minimize the impact of a data breach on your organization.
Like what you read?
About Mindsight
Mindsight, a Chicago IT services provider, is an extension of your team. Our culture is built on transparency and trust, and our team is made up of extraordinary people – the kinds of people you would hire. We have one of the largest expert-level engineering teams delivering the full spectrum of IT services and solutions, from cloud to infrastructure, collaboration to contact center. Our customers rely on our thought leadership, responsiveness, and dedication to solving their toughest technology challenges.
Contact us at GoMindsight.com.
About The Author
Mishaal Khan, Mindsight’s Security Solutions Architect, has been breaking and – thankfully – rebuilding computers for as long as he can remember. As a Certified Ethical Hacker (CEH), CCIE R&S, Security Practitioner, and Certified Social Engineer Pentester, Khan offers insight into the often murky world of cybersecurity. Khan brings a multinational perspective to the business security posture, and he has consulted with SMBs, schools, government institutions, and global enterprises, seeking to spread awareness in security, privacy, and open source intelligence.
Siobhan Climer, Science and Technology Writer for Mindsight, writes about technology trends in education, healthcare, and business. She writes extensively about cybersecurity, disaster recovery, cloud services, backups, data storage, network infrastructure, and the contact center. When she’s not writing tech, she’s reading and writing fantasy, gardening, and exploring the world with her twin daughters. Find her on twitter @techtalksio.

